
Mobile OAuth, Deep Links, and IPC Hardening: A 90‑Day Engineering Playbook
Explore a 90-day engineering playbook to enhance mobile OAuth security and prevent data leakage on Android and iOS platforms.
33 articles

Explore a 90-day engineering playbook to enhance mobile OAuth security and prevent data leakage on Android and iOS platforms.

Explore the critical vulnerabilities in iOS and Android that expose WebView sessions and app sandboxes, revealing key architectural defenses.
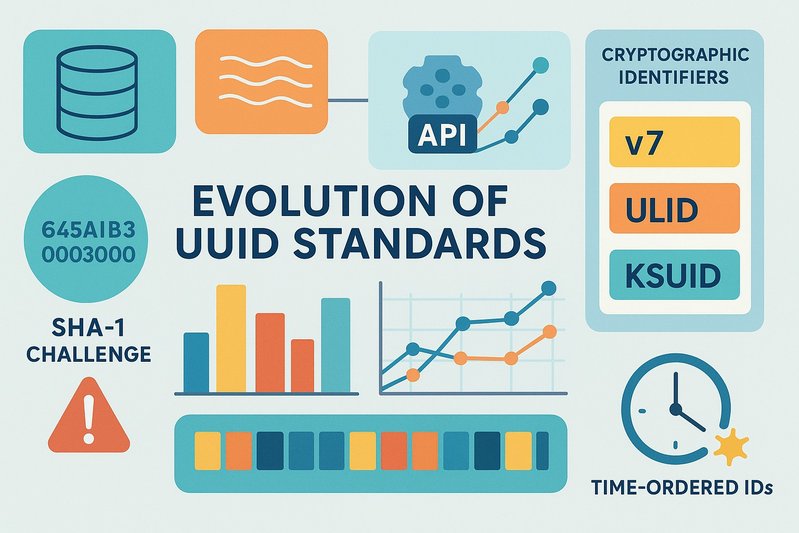
Explore how the 2024 IETF update impacts identifier design with SHA-1 challenges and new standards shaping cryptography and privacy.

Explore how HART's configurable thresholds are reshaping facial recognition risk profiles in ICE workflows and enhancing biometric security.

Explore the economic impact of Windows 11 OOB updates, focusing on ROI and compliance for security leaders navigating emergency patch challenges.

Explore Windows 11's January 2026 security updates focusing on identity, kernel integrity, and performance impacts of enforced protections.
Ad space (disabled)

Explore how Gotham Graph Analytics enhances ICE HSI's investigative capabilities with advanced data fusion and security measures for complex cases.
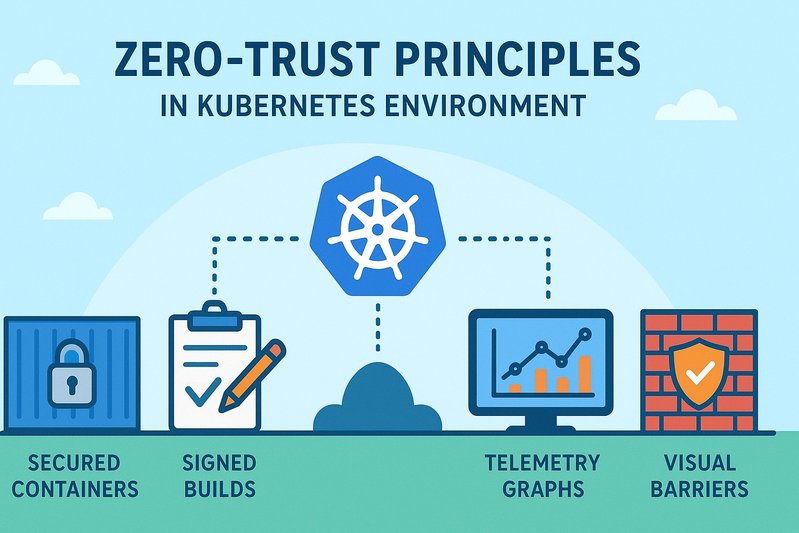
Explore zero-trust principles in Kubernetes for AI serving with signed builds, sandboxed pods, and real-time telemetry in this comprehensive guide.

Explore how confidential computing and content credentials secure generative media by enhancing trust and proving origin on a large scale.
Explore how enterprise risk governance translates diffusion security into measurable ROI, prioritizing threats and aligning controls in 2026.
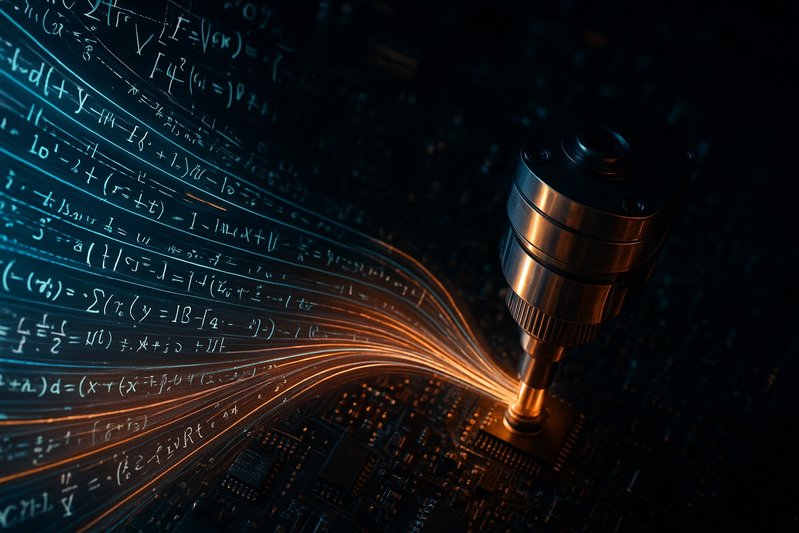
Explore how sampler integrity and CSPRNG isolation enhance the reliability of diffusion pipelines in AI, ensuring robust and tamper-resistant outputs.

Discover essential patterns for ensuring data integrity during complex cloud migrations to safeguard your business's vital information.
Ad space (disabled)

Explore secure migration strategies with effective testing methodologies and continuous verification throughout the software development lifecycle.

Explore effective change strategies for secure database schemas and API contracts to enhance compatibility and minimize downtime in modern IT systems.

Explore strategies for zero-downtime database and API migrations while ensuring robust cybersecurity in your digital transformation journey.
Explore how to secure AI collaboration in 2026 with post-quantum cryptography and hybrid solutions to face the quantum computing challenge.
Explore how encryption-centric AI workspaces are set to transform security and collaboration in professional environments by 2026.

Explore how the Supreme Court adapts IT governance policies to combat cyber threats and enhance security in judicial institutions.
Ad space (disabled)

Discover how post-2026 changes impact U.S. platforms' data privacy compliance amidst evolving legislation and judicial rulings.

Explore how the 2026 data breaches reshaped government cybersecurity, fostering technological innovations and regulatory changes to enhance protection.

Explore how Go integrates the OSV model for effective vulnerability management in development practices, ensuring security and sustainability.

Explore the future of real-time video analytics and its transformative impact across industries by 2026 with advanced AI systems and technologies.

Discover methods to secure and trace configuration changes in automated systems, ensuring integrity and zero downtime in evolving environments.

Explore strategies for securing the software supply chain in a zero-trust environment, focusing on robust security and compliance in modern ecosystems.
Ad space (disabled)

Explore the essentials of Security Exposure Management in 2026, focusing on robust frameworks and methods for continuous threat management.

Explore how strong networking and strict privacy measures unlock the transformative potential of augmented reality in our digital future.

Explore how robotics and drone technology are enhancing global defense capabilities and reshaping military operations in the modern era.

Explore common governance challenges in cloud accounts and learn solutions to enhance security and compliance for your cloud operations.
Learn how to use observability tools effectively to maintain performance and security during platform migrations.

Explore how privacy-preserving intelligence is reshaping technology, balancing powerful computation with essential privacy concerns in the digital age.
Ad space (disabled)

Explore privacy and security obligations for businesses as regulations evolve towards 2026, ensuring compliance across global jurisdictions.

Explore how architectural agnosticism is redefining security structures in a rapidly evolving digital landscape, ensuring safety and adaptability.
Explore the vital intersection of security and sustainability in AI/ML memory systems amid the rapid technological evolution.
Ad space (disabled)
Vous pouvez choisir quels cookies vous souhaitez autoriser. Certains cookies sont nécessaires au fonctionnement du site.
Ces cookies sont essentiels au fonctionnement du site (navigation, préférences de langue, etc.).
Nous aident à comprendre comment les visiteurs utilisent notre site pour l'améliorer.
Permettent d'afficher des publicités pertinentes. Requis pour afficher Google AdSense.